Industrial Cybersecurity: Key Concepts Based on IEC Standards
Operational Technology (OT) and Industrial Control Systems (ICS)
1. Understanding Industrial Control Systems (ICS)
Industrial environments rely on multiple critical assets:
- Field Devices (sensors & actuators)
- PLCs (Programmable Logic Controllers)
- HMIs (Human Machine Interfaces)
- Engineering Workstations
- Data Historians
- Safety Instrumented Systems (SIS)
PLCs are the core of automation and are typically programmed using Ladder Logic, defined under IEC 61131-3 .
2. IEC 62443 – The Foundation of Industrial Cybersecurity
The IEC 62443 standard provides a structured approach to securing industrial systems.
Seven Foundational Requirements (FR):
- Identification & Authentication Control – Verify all users and devices
- Use Control – Enforce least privilege access
- System Integrity – Prevent unauthorized changes
- Data Confidentiality – Protect sensitive information
- Restricted Data Flow – Segment networks (zones & conduits)
- Timely Response to Events – Detect and respond quickly
- Resource Availability – Ensure uptime, even during attacks
These are the backbone of any OT cybersecurity strategy.
3. Security Levels (SL) – Measuring Protection
IEC 62443 defines security levels based on threat sophistication:
- SL1 – Basic protection (accidental misuse, simple malware)
- SL2 – Protection against common attacks
- SL3 – Protection against advanced attackers
- SL4 – Protection against nation-state threats
It also introduces:
- SL-T (Target) – Desired security level
- SL-A (Achieved) – Current level
- SL-C (Capability) – Maximum supported level
4. Risk Assessment (Core of IEC 62443)
Cybersecurity in OT starts with risk assessment.
Key steps:
- Identify assets and communications
- Identify threats and vulnerabilities
- Assess impact (production, safety, cost)
- Calculate risk
- Compare with risk tolerance
- Apply countermeasures
This process is done using zones and conduits, a fundamental IEC 62443 concept.
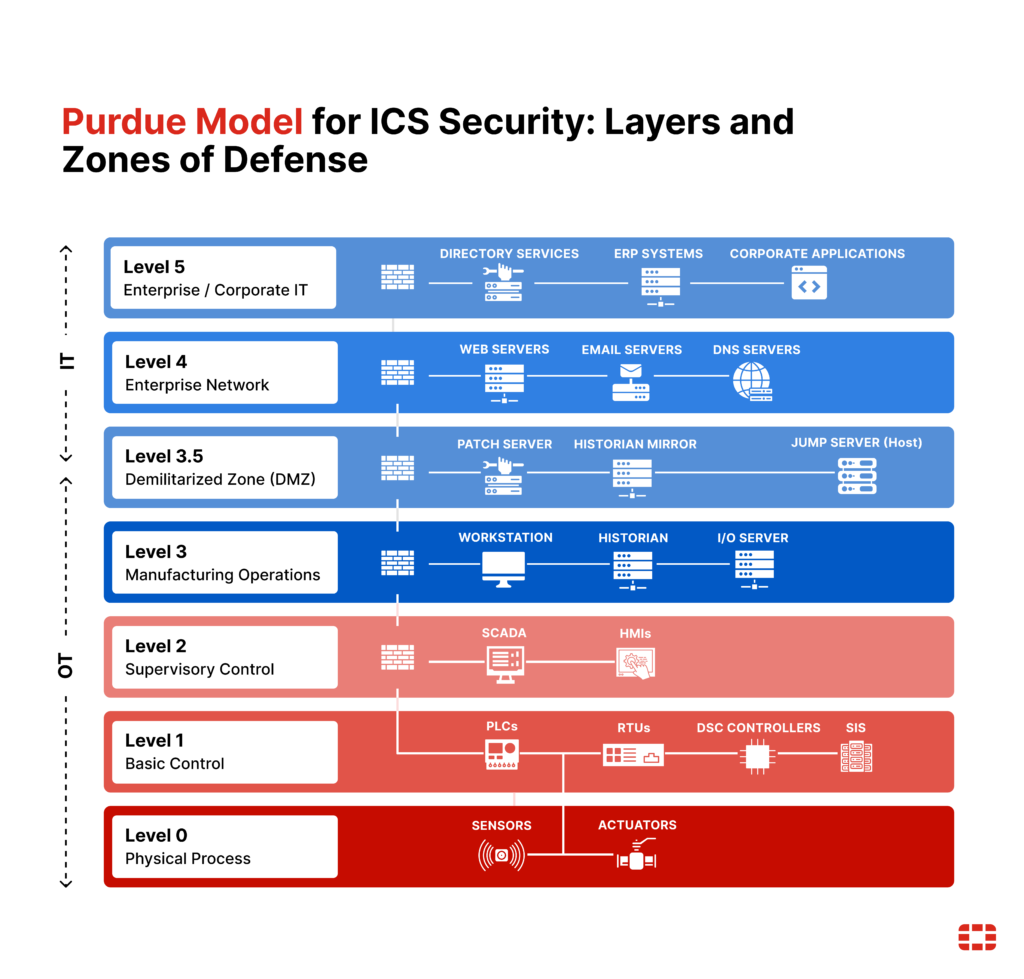
5. Network Segmentation & Secure Architecture
A secure OT network must follow:
- Zone segmentation (separate systems by function/criticality)
- Conduits (controlled communication paths)
- Defense-in-depth strategy
Example:
- Control network separated from IT
- DMZ used for external access
- Critical systems isolated
6. Remote Access Security (High-Risk Area)
Remote access is necessary but introduces major risks.
Best practices:
- Use jump servers
- Apply multi-factor authentication (MFA)
- Enforce least privilege
- Monitor and log all activity
- Use DMZ segmentation
7. Safety Systems Must Be Isolated (SIS)
Safety Instrumented Systems (SIS) require special protection:
- Must be physically separated (air-gapped)
- No shared networks with control systems
- No remote access
- Use one-way communication (data diodes)
This prevents catastrophic failures if the control system is compromised .
8. Business Impact of Cybersecurity
Cyber incidents in OT can lead to:
- Production downtime
- Financial losses
- Safety hazards
- Environmental damage
- Loss of trust and reputation
That’s why cybersecurity must align with business risk, not just technical controls.
Final Thoughts
Industrial cybersecurity is no longer optional—it is a critical component of modern automation systems. As industrial environments become more connected, the attack surface continues to grow, making structured security approaches essential.
Standards like IEC 62443 provide a clear framework to identify risks, define security levels, and implement effective protections across industrial systems. From proper network segmentation to strict access control and continuous monitoring, every layer contributes to a resilient and secure operation.
Ultimately, cybersecurity in OT is about more than protecting systems—it’s about ensuring safety, reliability, and business continuity.